Microsoft’s security patch to fix a critical flaw in its systems has made it less rather than more secure, researchers are warning.
News broke in January 2018 that a in-built weakness in Intel computer chips and ARM smartphone chips could affect billions of devices, from laptops to the hardware that powers server farms and data centres.
Google’s Project Zero security researchers found that the bugs, dubbed Meltdown and Spectre, were side-channel attacks against CPU microprocessors that allow code to read data it should not have access to.
The Spectre of doom
The threat is so great that the UK’s cybersecurity lead at the National Cyber Security Centre – part of GCHQ – issued this warning: “Processors in most devices employ a range of techniques to speed up their operation. The Meltdown and Spectre vulnerabilities allow some of these techniques to be abused, in order to obtain information about areas of memory not normally visible to an attacker. This could include secret keys or other sensitive data.
“In the worst case, code running on a device can access areas of memory it does not have permission to access. This can result in compromise of sensitive data, including secret keys and passwords.”
Meltdown affects laptops, desktop computers and internet servers with Intel chips, while Spectre affects some chips in smartphones, tablets and computers powered by Intel, ARM and AMD.
Nigel Houden, the head of technology policy for the UK’s Information Commission Office (ICO) explains the flaw: “In essence, the vulnerabilities provide ways that an attacker could extract information from privileged memory locations that should be inaccessible and secure.
“Depending on the specific circumstances an attacker could gain access to encryption keys, passwords for any service being run on the machine, or session cookies for active sessions within a browser.
“The implications for data controllers are clear. If these vulnerabilities are exploited on a system that is processing personal data, then that personal data could be compromised.
“Alternatively, an attacker could steal credentials or encryption keys that would allow them to access personal data stored elsewhere.”
But while manufacturers have been scrambling to produce fixes, their efforts are producing more vulnerabilities rather than fewer.
Microsoft make Windows 7 leak
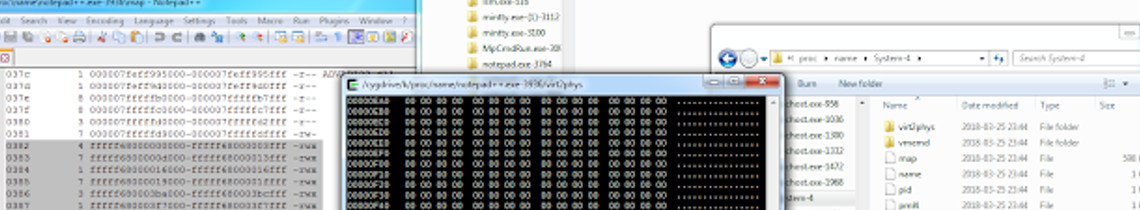
Ulf Frisk, an independent cybersecurity researcher, discovered that while fixing the defect for Windows 7. Microsoft opened up a whole host of other problems.
He writes: “Did you think Meltdown was bad? Unprivileged applications being able to read kernel memory at speeds possibly as high as megabytes per second was not a good thing.
“Meet the Windows 7 Meltdown patch from January.
“It stopped Meltdown but opened up a vulnerability way worse … It allowed any process to read the complete memory contents at gigabytes per second, oh – it was possible to write to arbitrary memory as well.”
It’s understood that the problem affects machines running the 64-bit version of Windows 7 or Windows Server 2008 R2.
Microsoft issued a statement to SecurityWeek to say they are aware of the issue, with security teams looking closely for a fix.
MAIN IMAGE: Ulf Frisk