It’s a truism of protecting your devices and your data to avoid connecting to insecure public WiFi and to password-protect everything up to the hilt.
But it could all be for naught according to one security researcher.
PhD student Mathy Vanhoef probed the main technology used to provide UK WiFi – WPA2 – and discovered a serious weakness.
This video demonstration posted to Youtube of his attack has already amassed nearly 900,000 views.
His slightly terrifying assessment find that if your device uses WiFi, whether that’s a phone, a tablet, a laptop or PC, it is probably vulnerable.
We’ll just repeat that. Every device. Probably vulnerable.
First of all, if you’re relying on something as potentially insecure as public Wi-Fi, you should always use protection in the form of a VPN.
A VPN will allow you to browse securely and anonymously as it disguises your true IP address from anyone illegally listening in to the network.
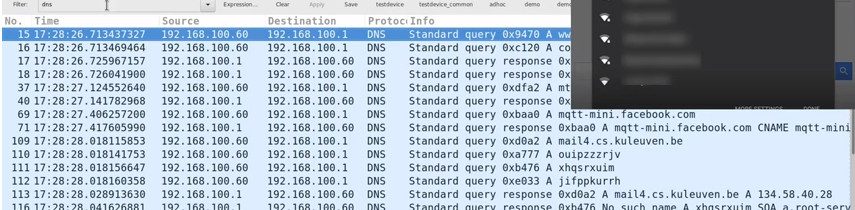
Vanhoef’s demonstration shows how easily he is able to bypass WPA2, a protocol that is supposed to secure all current WiFi networks.
He says: “An attacker within range of a victim can exploit these weaknesses using Key Reinstallation Attacks (KRACKs)” to read encrypted data.
The list of what’s easily available to hackers using this technique is horrifying.
Credit card numbers, passwords, instant message chats, emails, photos or any personal data on your device would be up for grabs.
The weakness is in WPA2 itself, not the way this protocol is used by specific networks, so “any correct implementation of WPA2 is likely to be affected”.
According to this list, Apple, Google, Sony and Samsung Mobile are among the companies to have already issued updates to combat the weakness, but many more vendors, including Blackberry, Ericsson, HTC and Huawei have the status ‘Unknown’.
Patches will work, says Vanhoef, and you don’t immediately need WPA3. You can carry on using WiFi but you should update all your devices to the latest software available.
Should you update your WiFi password?
While updating your WiFi password won’t prevent a KRACK attack from being successful, it’s never a bad idea.
What is really important, Vanhoef says, is to make sure all your devices are updated, and update your router’s firmware.
Go deeper
The full research paper was presented at the Computer and Communications Security conference in Dallas, Texas, on 1 November 2017.
It’s available to read at krackattacks.com.